The fileless code injection technique called Process Doppelgänging is actively being used by not just one or two but a large number of malware families in the wild, a new report shared with The Hacker News revealed.
Discovered in late 2017, Process Doppelgänging is a fileless variation of Process Injection technique that takes advantage of a built-in Windows function to evade detection and works on all modern versions of Microsoft Windows operating system.
Process Doppelgänging attack works by utilizing a Windows feature called Transactional NTFS (TxF) to launch a malicious process by replacing the memory of a legitimate process, tricking process monitoring tools and antivirus into believing that the legitimate process is running.
Few months after the disclosure of this technique, a variant of the SynAck ransomware became the first-ever malware exploiting the Process Doppelgänging technique, targeting users in the United States, Kuwait, Germany, and Iran.
Shortly after that, researchers discovered a dropper (loader) for the Osiris banking trojan that was also using this technique in combination with a previously discovered similar malware evasion technique called Process Hollowing.
Now, turns out that it was not just SynAck or Osiris, but more than 20 different malware families—including FormBook, LokiBot, SmokeLoader, AZORult, NetWire, njRat, Pony stealer, and GandCrab ransomware—have been using malware loaders that leverage this hybrid implementation of Process Doppelgänging attack to evade detection.
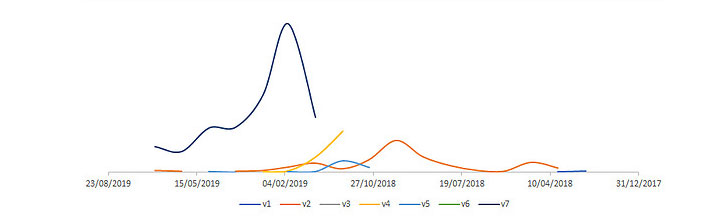
After analysing hundreds of malware samples, security researchers at enSilo discovered at least seven distinct versions of such loader, which they dubbed “TxHollower,” used by various malware authors.
“Attackers are known to reuse resources and tools in their attack chains, most notable are droppers, packers, and loaders. It highlights that shared components and code make tracking and attributing various groups even more complicated,” researchers said.
Researchers believe TxHollower loaders are available to cybercriminals through some offensive framework or exploit kit, eventually increasing the use of process doppelgänging-like techniques in-the-wild.
The earliest sample of the loader with TxHollower feature was used in March 2018 to distribute Netwire RAT, and then later also found bundled with multiple GandCrab versions, starting with v5 and going all the way to v5.2.
Besides this, researchers at enSilo also found a few samples wrapped in an additional layer such as MSI files and in some cases, loaders were nested with each other.
“While we didn’t observe the actual infections, we were able to find a few samples we suspect to be related to the infection chain like downloaders and droppers of TxHollower. The type of files include PE executables, JavaScript and documents,” the researchers said.
To learn more about how the Process Doppelgänging attack technique works, you can read the previous article we published in 2017, and if you want to know more about various versions of TxHollower loader, you can head straight on to enSilo blog post published today.