A Russian-speaking ransomware outfit likely targeted an unnamed entity in the gambling and gaming sector in Europe and Central America by repurposing custom tools developed by other APT groups like Iran’s MuddyWater, new research has found.
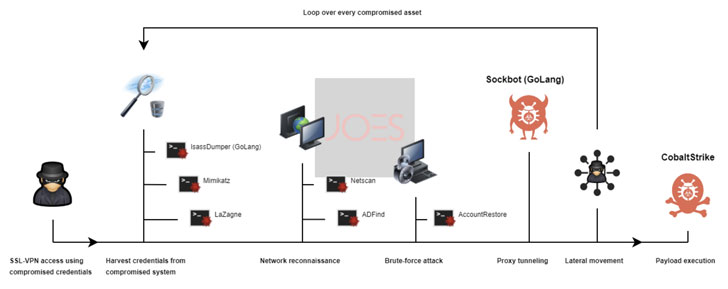
The unusual attack chain involved the abuse of stolen credentials to gain unauthorized access to the victim network, ultimately leading to the deployment of Cobalt Strike payloads on compromised assets, said Felipe Duarte and Ido Naor, researchers at Israeli incident response firm Security Joes, in a report published last week.
Although the infection was contained at this stage, the researchers characterized the compromise as a case of a suspected ransomware attack.
The intrusion is said to have taken place in February 2022, with the attackers making use of post-exploitation tools such as ADFind, NetScan, SoftPerfect, and LaZagne. Also employed is an AccountRestore executable to brute-force administrator credentials and a forked version of a reverse tunneling tool called Ligolo.
Called Sockbot, the modified variant is a Golang binary that’s designed to expose internal assets from a compromised network to the internet in a stealthy and secure manner. The changes made to the malware remove the need to use command-line parameters and includes several execution checks to avoid running multiple instances.
Given that Ligolo is a primary tool of choice for the Iranian nation-state group MuddyWater, the use of a Ligolo fork has raised the possibility that the attackers are taking tools used by other groups and incorporating their own signatures in a probable attempt to confuse attribution.
The links to a Russian-speaking ransomware group come from artifact overlaps with common ransomware toolkits. Furthermore, one of the deployed binaries (AccountRestore) contains hard-coded references in Russian.
“The strategy used by threat actors to access and pivot over the victim’s infrastructure lets us see a persistent, sophisticated enemy with some programming skills, red teaming experience and a clear objective in mind, which is far from the regular script kiddie profile,” the researchers said.
“The fact that the entry point for this intrusion was a set of compromised credentials reassures the importance of applying additional access controls for all the different assets in any organization.”