Threat actors have begun to use the Tox peer-to-peer instant messaging service as a command-and-control method, marking a shift from its earlier role as a contact method for ransomware negotiations.
The findings from Uptycs, which analyzed an Executable and Linkable Format (ELF) artifact (“72client“) that functions as a bot and can run scripts on the compromised host using the Tox protocol.
Tox is a serverless protocol for online communications that offers end-to-end encryption (E2EE) protections by making use of the Networking and Cryptography library (NaCl, pronounced “salt”) for encryption and authentication.
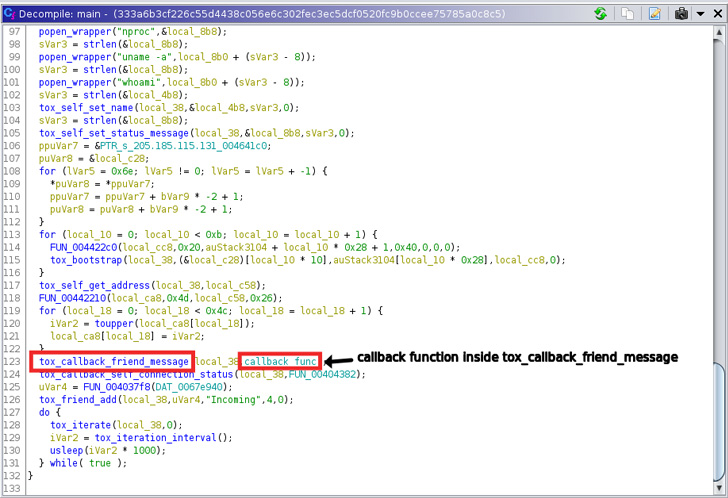
“The binary found in the wild is a stripped but dynamic executable, making decompilation easier,” researchers Siddharth Sharma and Nischay Hedge said. “The entire binary appears to be written in C, and has only statically linked the c-toxcore library.”
It’s worth noting that c-toxcore is a reference implementation of the Tox protocol.
The reverse engineering undertaken by Uptycs shows that the ELF file is designed to write a shell script to the location “/var/tmp/” – a directory used for temporary file creation in Linux – and launch it, enabling it to run commands to kill cryptominer related processes.
Also executed is a second routine that allows it to run a number of specific commands (e.g., nproc, whoami, machine-id, etc.) on the system, the results of which are subsequently sent over UDP to a Tox recipient.
Additionally, the binary comes with capabilities to receive different commands through Tox, based on which the shell script is updated or gets executed on an ad-hoc basis. An “exit” command issued quits the Tox connection.
Tox has been historically used by ransomware actors as a communication mechanism, but the latest development marks the first time the protocol is being used to run arbitrary scripts on an infected machine.
“While the discussed sample does not do anything explicitly malicious, we feel that it might be a component of a coinminer campaign,” the researchers said. “Therefore, it becomes important to monitor the network components involved in the attack chains.”
The disclosure also arrives amid reports that the decentralized file system solution known as IPFS is being increasingly used for hosting phishing sites in an effort to make takedowns more difficult.