Making the most of newly disclosed and even patched vulnerabilities has develop into widespread amongst cybercriminals, which makes it one of many major assault vectors for everyday-threats, like crypto-mining, phishing, and ransomware.
As suspected, a recently-disclosed crucial vulnerability within the broadly used Oracle WebLogic Server has now been noticed actively being exploited to distribute a never-before-seen ransomware variant, which researchers dubbed “Sodinokibi.”
Final weekend, The Hacker Information realized a few crucial deserialization distant code execution vulnerability in Oracle WebLogic Server that might permit attackers to remotely run arbitrary instructions on the affected servers simply by sending a specifically crafted HTTP request—with out requiring any authorization.
To deal with this vulnerability (CVE-2019-2725), which affected all variations of the Oracle WebLogic software program and was given a severity rating of 9.eight out of 10, Oracle rolled out an out-of-band security update on April 26, only a day after the vulnerability was made public and a number of other in-the-wild assaults had been noticed.
In accordance with cybersecurity researchers from Cisco Talos’ menace analysis group, an unknown group of hackers has been exploiting this vulnerability since at the very least April 25 to contaminate weak servers with a brand new piece of ransomware malware.
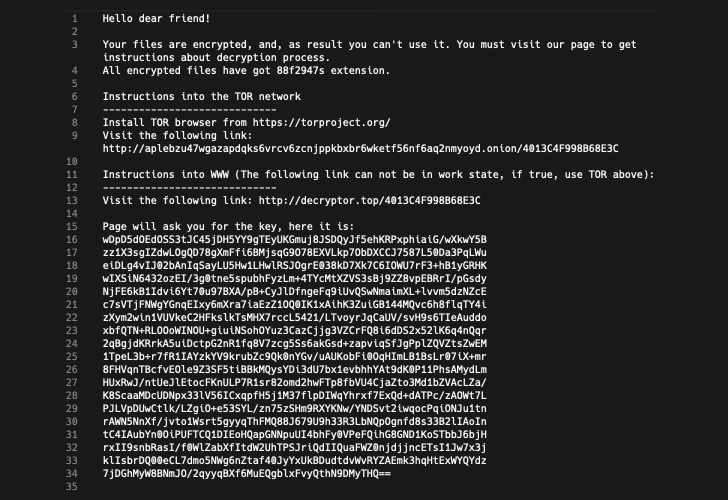
Sodinokibi is a harmful ransomware variant which has been designed to encrypt recordsdata in a person’s listing after which delete shadow copy backups from the system in an effort to forestall victims from recovering their knowledge with out paying a ransom.
No Interplay Required to Deploy Ransomware
Since attackers are leveraging a distant code execution vulnerability within the WebLogic Server, in contrast to typical ransomware assaults, deploying the Sodinokibi ransomware requires no person interplay.
“Traditionally, most forms of ransomware have required some type of person interplay, reminiscent of a person opening an attachment to an electronic mail message, clicking on a malicious hyperlink, or working a chunk of malware on the machine,” researchers clarify in a blog post.
“On this case, the attackers merely leveraged the Oracle WebLogic vulnerability, inflicting the affected server to obtain a duplicate of the ransomware from attacker-controlled IP addresses.”
As soon as downloaded, the Sodinokibi ransomware encrypts the sufferer’s techniques and shows a ransom observe demanding as much as $2,500 in Bitcoin. The quantity doubles to $5,000 if the ransom just isn’t paid inside a specified variety of days—which can range from two days to 6 days.
Hackers Are Additionally Putting in GandCrab Ransomware
Researchers additionally famous that roughly eight hours after deploying Sodinokibi on an contaminated system, the attackers exploited the identical WebLogic Server vulnerability to put in one other piece of ransomware generally known as GandCrab (v5.2).
“We discover it unusual the attackers would select to distribute further, totally different ransomware on the identical goal,” the researchers say. “Sodinokibi being a brand new taste of ransomware, maybe the attackers felt their earlier makes an attempt had been unsuccessful and had been nonetheless trying to money in by distributing Gandcrab.”
Attackers have been exploiting the Oracle WebLogic Server vulnerability within the wild since at the very least April 17 to distribute cryptocurrency miners and different types of malware.
WebLogic Server is a well-liked Java-based multi-tier enterprise utility server usually utilized by companies to assist enterprise apps, which makes it an usually goal of attackers making an attempt to hold out malicious operations, like working cryptocurrency miners and infecting with ransomware.
Organizations that use Oracle WebLogic Server ought to ensure to replace their installations to the most recent model of the software program as quickly as potential.