Researchers have discovered a new adware variant that is capable of escaping antivirus detection. The DealPly adware possesses traits to bypass security measures. The adware abuses McAfee and Microsoft reputation services to elude detection.
DealPly Adware Evades Detection
Reportedly, researchers from Ensilo have presented their analysis regarding a new adware variant. Termed DealPly, the adware seamlessly avoids antivirus detection by abusing reputation services. The researchers elaborated their findings in a recent blog post.
As explained, the malware bears numerous features to dodge security protocols. These include VM detection, fingerprinting, and abusing Microsoft SmartScreen and McAfee WebAdvisor services to skip detection.
Delving into the technicalities associated with this malware reveals that the adware basically comprises of numerous modules that work in three different stages to execute the attack.
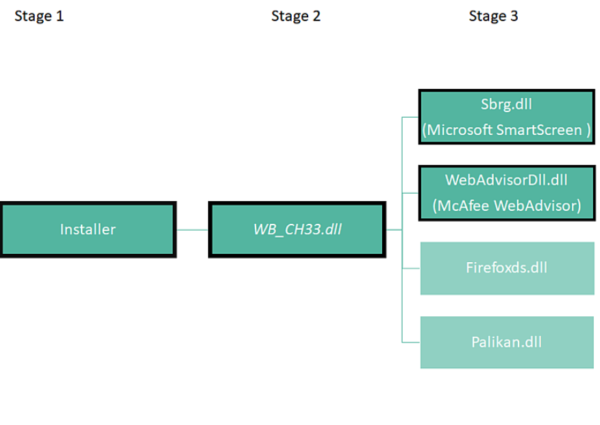
The most important of these modules is “WB_CH33.dll” which carries the core functionalities of the malware. It commands and executes the other modules, and performs a geolocation check to save country codes.
The DealPly attack begins when the adware reaches the victim device via otherwise legitimate software installers from services. The researchers caught this adware coupled with the installer for the photo-editing software ‘Fotor’.
The adware executes together with the installer as part of the installation process. It then replicates itself on the AppData directory and Windows Task Scheduler. This allows the adware to execute on an hourly basis, sending encrypted requests over HTTP to the C&C every time. The main module “WB_CH33.dll” receives the subsequent commands.
Once a valid request is sent to the server, It will respond with redirecting the client to d1oz9ywjzmvfb5.cloudfront.net. This domain is pointing at one of Amazon’s S3 servers. The response contains instructions as well as the main module to be executed.
During this process, the adware also sends data to the C&C regarding VM detection and host fingerprinting.
Strategy To Evade Detection
As stated above, DealPly abuses Microsoft SmartScreen and McAfee WebAdvisor to remain undetected. Regarding the abuse of these services, the researchers stated in their blog post,
Microsoft SmartScreen and McAfee WebAdvisor provide threat intelligence verdicts on files and URLs and are free to use. With the data from these services, the life-span for the Adware’s installers and components can be prolonged as changes are required only once they are known to be blacklisted.
This constant querying enables the attackers to spot the adware’s detection rate by antivirus and create new samples when required. Thus, the malware attack becomes difficult to detect and stop.
The researchers fear that such evasive strategy may trigger advanced malware campaigns as well.
Let us know your thoughts in the comments.

